demonstrate the feasibility of the attacks, we developed a proof-of-concept Android application. Our app implements the attacks as man-in-the-middle attacks built on top of a relay attack architecture, using two NFC-enabled phones.
EMV, named after its founders Europay, Mastercard, and Visa, is the international protocol standard for in-store smartcard payment. In December 2020, EMVCo reported 9.89 billion EMV cards in circulation worldwide. Despite the standard’s advertised security, various issues have been previously uncovered, deriving from logical flaws that are hard to spot in EMV’s lengthy and complex specification, running over 2,000 pages.
We have specified a comprehensive model of the EMV protocol, using the Tamarin model checker. Using our model, we identified several authentication flaws that lead to two critical attacks: one affecting Visa cards and another affecting Mastercard cards.
The attack on Visa allows criminals to complete a purchase over the PIN-less limit with a victim’s Visa contactless card without knowing the card’s PIN. In other words, the PIN in your Visa card is useless as it won’t protect your card from being used for fraudulent, high-value purchases.
The attack on Mastercard allows criminals to trick a terminal into transacting with a victim’s Mastercard contactless card while believing it to be a Visa card. This card brand mixup has critical consequences since it can be used in combination with the PIN bypass for Visa to also bypass the PIN for Mastercard cards. As a result of our disclosure process, Mastercard has since implemented defense mechanisms, which we experimentally confirmed as effective against the attack.
Demonstrating the attacks
To demonstrate the feasibility of the attacks, we developed a proof-of-concept Android application. Our app implements the attacks as man-in-the-middle attacks built on top of a relay attack architecture, using two NFC-enabled phones.
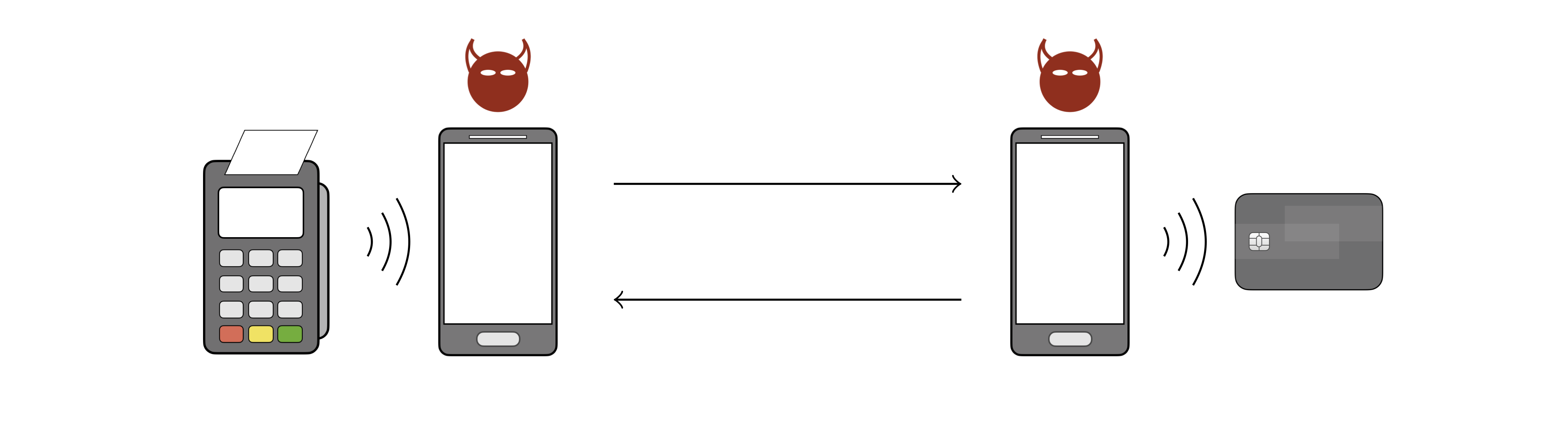
The outermost devices are the payment terminal (on the left) and the victim’s contactless card (on the right). The phone near the payment terminal is the attacker’s card emulator device and the phone near the victim’s card is the attacker’s POS emulator device. The attacker’s devices communicate with each other over WiFi, and with the terminal and the card over NFC.
For the attacks to work, the criminals must have access to the victim’s card, either by stealing it, finding it if lost, or by holding the POS emulator near it if still in the victim’s possession. The attacks work by modifying the terminal’s commands and the card’s responses before delivering them to the corresponding recipient.
Our app does not require root privileges or any hacks to Android. We have used it on Google Pixel 2 XL and Huawei P Smart 2019 devices.
Attack on Visa
The attack consists in a modification of the Card Transaction Qualifiers (CTQ, a card-sourced data object), before delivering it to the terminal. The modification instructs the terminal that:
- PIN verification is not required, and
- the cardholder was verified on the consumer’s device (e.g., a smartphone).
We have successfully tested this attack with Visa Credit, Visa Debit, Visa Electron, and V Pay cards. A video demonstration for a 200 CHF transaction is given below.
This attack may also affect Discover and UnionPay cards. Our findings have been covered by ETH Zurich, ACM TechNews, Schweizer Radio und Fernsehen (SRF), The Hacker News, ZDNet, heise, and a full technical report is given in our paper:
David Basin, Ralf Sasse, and Jorge Toro-Pozo
42nd IEEE Symposium on Security and Privacy (S&P), 2021
PDF (arXiv) | DOI | BibTex | Tamarin model
Attack on Mastercard
This attack primarily consists in the replacement of the card’s legitimate Application Identifiers (AIDs) with the Visa AID A0000000031010
to deceive the terminal into activating the Visa kernel. The attacker
then simultaneously performs a Visa transaction with the terminal and a
Mastercard transaction with the card. In the Visa transaction, the
attacker applies the aforementioned attack on Visa.
For this attack to work, the terminal’s authorization request must reach the card-issuing bank. Requirements for this include:
- the terminal does not decline offline even if the card number (PAN) and the AIDs indicate different card brands, and
- the merchant’s acquirer routes the transaction authorization request to a payment network that can process Mastercard cards.
We have successfully tested this attack with Mastercard Credit and Maestro cards. A video demonstration for a 400 CHF transaction is given below.
This attack may also affect JCB and American Express cards. Our research has been featured by ETH Zurich, ACM TechNews, The Hacker News, and a full technical report is given in our paper:
Bypassing the PIN in non-Visa cards by Using Them for Visa Transactions
David Basin, Ralf Sasse, and Jorge Toro-Pozo
30th USENIX Security Symposium, 2021
PDF | BibTex | Tamarin model
FAQ
What cards are affected by these attacks?
We have successfully bypassed the PIN for Visa Credit, Visa Debit, Visa Electron, V Pay, Mastercard Credit, and Maestro cards. Further EMV cards may be affected but we have no proof of this in the wild.
Has there been any response by the affected companies?
What role did Tamarin play in this research?
There have been many attacks on EMV before, what makes these different?
What went wrong? How can such problems be avoided in the future?
Should we protect our cards in a “metal wallet” to prevent them being read remotely?
This might help. Although you still have problems if they are lost or stolen.
What actions should I as a citizen take now to protect myself?
Protection measures recommended by banks apply. Block your card immediately upon realization it is lost or stolen. Check your bank statement regularly, and immediately report to your bank whenever you see an unrecognized transaction. Additionally, whenever you are carrying an EMV contactless card, make sure nobody is holding a device near it against your will. Also, be aware of your back pocket.
Where do I find the Android app?
Nowhere. We do not make it available.
Team
Prof. Dr. David Basin
Dr. Ralf Sasse
Dr. Jorge Toro
Institute of Information Security
Department of Computer Science
ETH Zurich
Comments
Post a Comment